Events
Limited-Trust in Diffusion of Competing Alternatives Over Social Networks & Apurv Shukla (Texas A&M University) – Differentially Private Online Resource Allocation
Limited-Trust in Diffusion of Competing Alternatives Over Social Networks & Apurv Shukla (Texas A&M University) – Differentially Private Online Resource Allocation
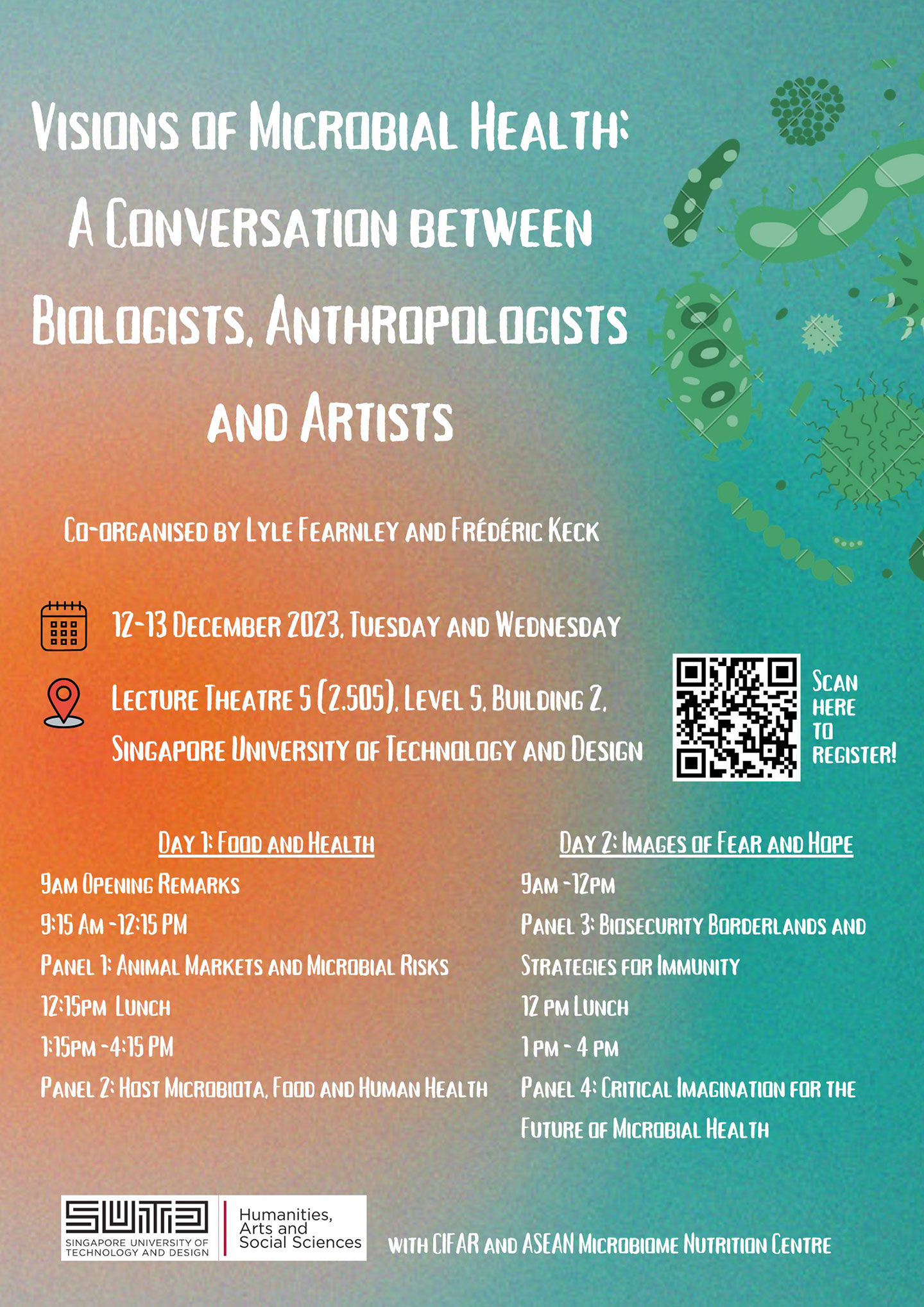
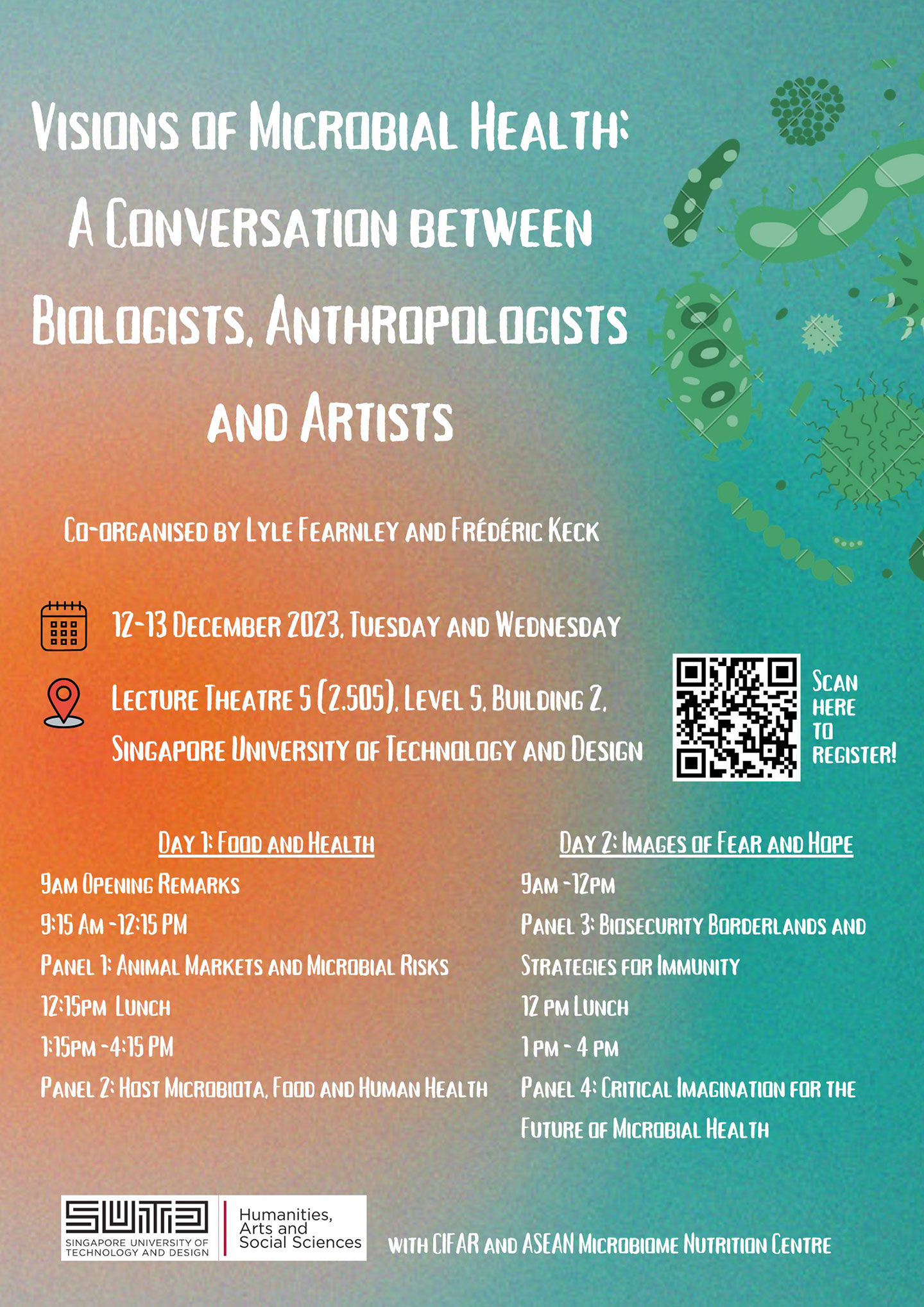
HASS Workshop: Visions of Microbial Health: A Conversation between Biologists, Anthropologists and Artists
From viruses that cause zoonotic pandemics to the gut microbes that condition metabolism inside the body, microbes play crucial roles in human health and disease. Increasingly powerful scientific techniques are bringing to light the microbes inside and outside of our bodies and revealing how microorganisms connect individuals and even cross species.
But what to do about the microbes that we live with is a question that cannot be answered by microbiological tools alone. The human impact on the environment, including the consumption of antibiotics that alter the microbiome or the deforestation that increases the risk of emerging pathogens, demands historical and cultural analysis. Calls for closure of wet markets or culling of infected livestock in order to control pathogen spillover raise important questions about cultural differences in human-nonhuman relationships, the evaluation of risk, and the valuation of nonhuman life. Artists and anthropologists provide new tools to help us see the many possibilities of human life amidst the microbiome. After a century of intensive antibiotic use in healthcare and the livestock industry, can we imagine co-existence with microbes? How can we increase public understanding of the microbiome and its impacts on health and environment? What new alliances can be envisioned between microbial cultures and human cultures?
This workshop will initiate a conversation between biologists, anthropologists and artists to discuss venues of critical thinking on relations between microbes and health in a rapidly changing planet. The meeting will provide inspiration for an exhibition project and a collaborative white paper that aim for a reflexive account of microbial cultures.
Nguyen Huu-Hai (Standard Chartered) – Functional Programming in Financial Markets
In this talk we showcase the application of functional programming in a very large industrial setting.
Hank Tang & Denghui Yao (LightSpeed Studios Singapore) – How to Develop a Video Game in Real Life? – from the industry perspective
In this sharing session, speakers will explore the key elements and principles that go into creating a successful video game, drawing from real-world examples and industry insights.
Robin Foe & Tham Hon Hoe (OCBC Bank) – OCBC Cloud Native Journey
Cloud native is an approach of building, deploying, and managing modern application at scale. Customers in modern digital banking demand a better banking experience with rich features that are personalised towards their lifestyle. To cope with such demand, organisations use modern tools and techniques that inherently support application development in agile infrastructure. These tools and techniques provide fast and frequent changes to application and improve speed to market.
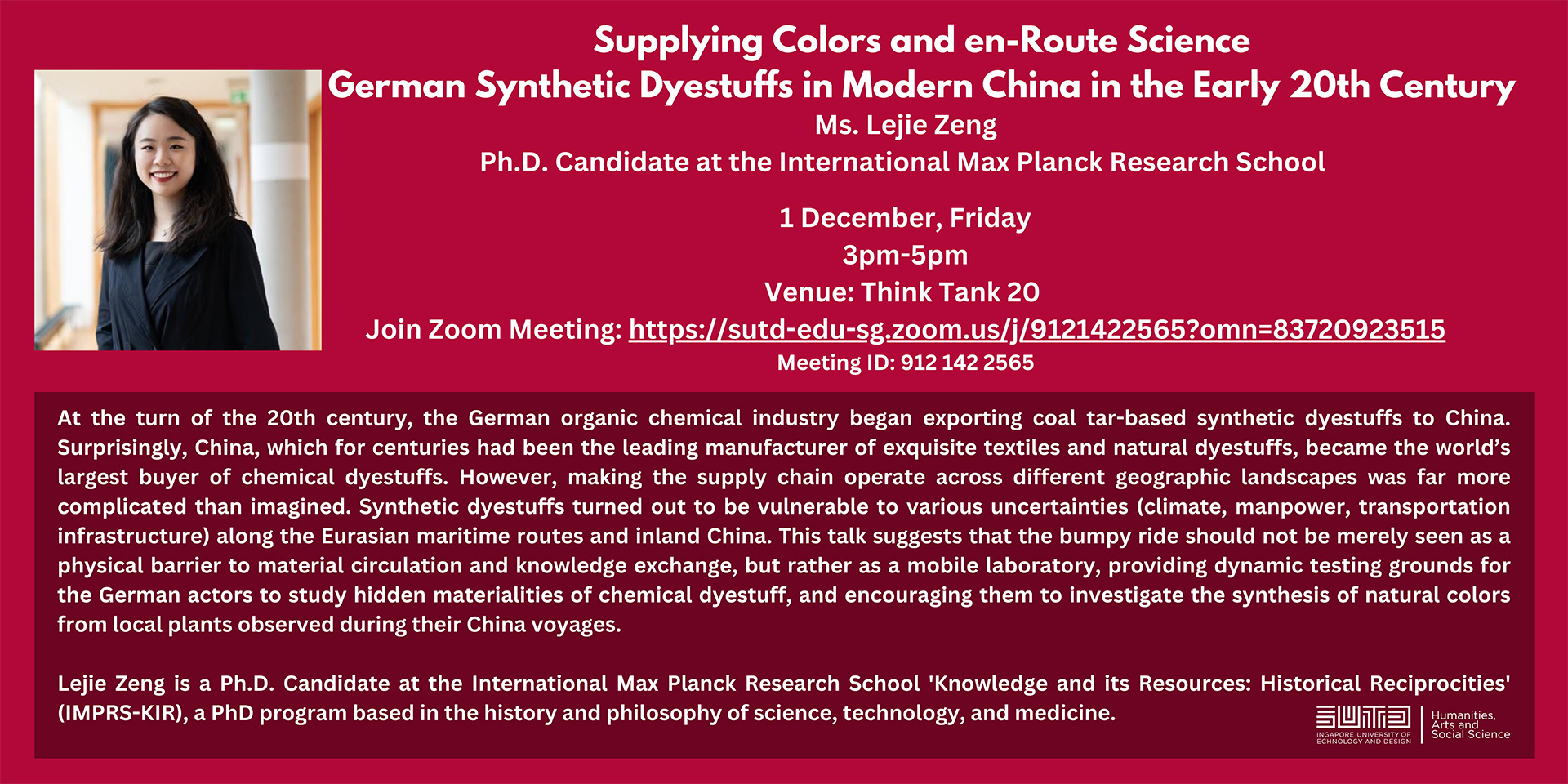
HASS Colloquium Series: Supplying Colors and en-Route Science: German Synthetic Dyestuffs in Modern China in the Early 20th Century by Ms. Lejie Zeng
At the turn of the 20th century, the German organic chemical industry began exporting coal tar-based synthetic dyestuffs to China.
Yan Shuo Tan (National University of Singapore) – Understanding and Overcoming the Statistical Limitations of Decision Trees
Yan Shuo Tan (National University of Singapore) – Understanding and Overcoming the Statistical Limitations of Decision Trees
Kendrik Tan & Selvi Yang (NCS Group) – Unboxing UX Design: The Art and Science
Join us for a guest lecture on UX design that explores the dynamic processes behind creating exceptional user experiences across a spectrum of technologies.
Anish Agarwal (Columbia University) – Causal Tensor Completion
Anish Agarwal (Columbia University) – Causal Tensor Completion
Yethoven Tukimin (Meta) – Building Immersive Future of Work
Immersive future of work is transforming how employees work, developing the next generation of innovation and redefining what customer engagement can be. Get a glimpse of what the next era of computing will look like and how you can be part of this exciting journey.