CoToRu: automatic generation of intrusion detection rules from programmable logic controller code
CoToRu: automatic generation of intrusion detection rules from programmable logic controller code
Technology title
CoToRu: automatic generation of intrusion detection rules from programmable logic controller code
Technology overview
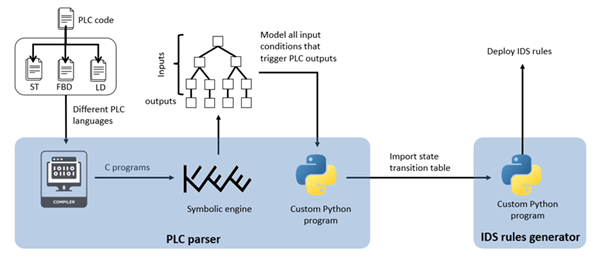
This technology is a toolchain that takes the Programmable Logic Controller (PLC) code as input to automatically generate a comprehensive set of intrusion detection system (IDS) rules. CoToRu consists of two components:
- an analyser that parses the PLC code to build a state transition table for modelling the PLC’s behaviour, and
- generator that instantiates IDS rules for detecting deviations in PLC behaviour.
CoToRu can detect various types of attacks while eliminating potential false alarms that may arise due to the IDS’s lack of visibility into the PLC’s internal processing state. The technology has been applied to a high-fidelity power grid testbed and shown to generate IDS rules that outperform existing IDS approaches, including those based on statistical analysis, invariant checking, and machine learning.
Technology specifications
The technology models PLC control logic as a decision tree and derives a state transition table by jointly capturing information technology and operational technology aspects. Device configuration files are used to map PLC variables to network messages, enabling accurate representation of control logic behaviour. Based on the resulting state transition table, the technology automatically generates IDS rules to detect message injection, deletion, delay, and modification caused by compromised PLCs. These rules can be directly deployed into the open source Zeek IDS for real-time detection. An automated rule-generation algorithm ensures consistent and scalable protection against control logic–level attacks.
Sector
This invention can be implemented in critical infrastructure protection, including industrial control systems (ICS) across sectors such as energy, transportation, maritime, manufacturing, and smart buildings.
Market opportunity
PLCs are widely deployed to control actuators such as motors and valves and are increasingly exposed through remote access software, authenticated control protocols, and inter-device communication networks. High-profile incidents such as Stuxnet have demonstrated the severe operational and economic impact of PLC-level attacks. There is a strong market demand for automated, accurate, and deployable solutions that can detect such attacks at the control-logic level.
Applications
Key applications include deployment in critical infrastructure systems, where practitioners can use the technology to generate intrusion detection system rules in Zeek format by supplying relevant system and configuration documents. Any ICS environment that deploys sensors, actuators, and PLCs can be supported.
Customer benefits
This technology reduces the time and effort required to design and deploy intrusion detection systems by automatically generating detection rules from PLC code. By leveraging an accurate representation of control logic behaviour, it improves detection accuracy while minimising false alarms and enables effective detection of sophisticated PLC-targeted cyberattacks. The automated and scalable rule-generation process supports faster security deployment across industrial environments and timely response to emerging and evolving threats.
Technology readiness level
TRL 5
Ideal collaboration partner
Ideal collaboration partners include:
- Critical infrastructure operators
- ICS security solution providers
- System integrators and automation vendors
Collaboration mode
This technology is suitable for multiple collaboration modes, including R&D collaboration, licensing, and IP acquisition.
