Scanning the cycle: fingerprinting the programmable logic controllers based on the scan cycle
Scanning the cycle: fingerprinting the programmable logic controllers based on the scan cycle
Technology title
Scanning the cycle: fingerprinting the programmable logic controllers based on the scan cycle
Technology overview
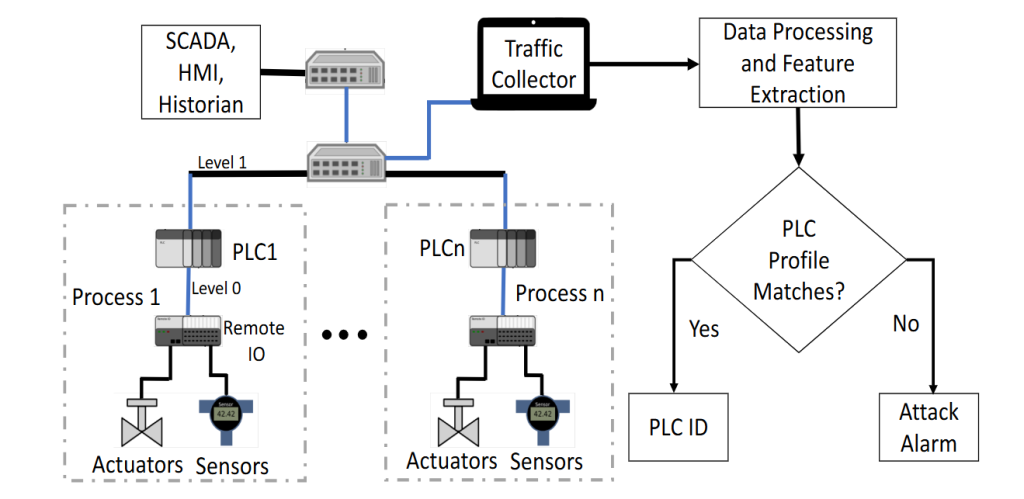
This technology proposes a non-invasive timing-based authentication technique for Programmable Logic Controllers (PLCs) used in Industrial Control Systems. Recognising that PLCs are critical real-time decision-making components that may be compromised or impersonated through spoofed network commands, the solution leverages the inherent scan cycle behaviour of each PLC as a unique fingerprint. By estimating scan cycle timing from network message exchanges, the system generates distinctive timing-based fingerprints that enable controller authentication and attack detection. Deviations from established fingerprints indicate potential command injection or spoofing attempts. Even advanced attackers attempting to imitate legitimate scan cycles can be detected due to unavoidable hardware-induced delays and imperfections. The approach has been experimentally validated on an operational water treatment testbed (SWaT), demonstrating reliable PLC differentiation and attack detection capabilities without modifying existing controller hardware.
Technology specifications
A PLC consists of a central processing unit (processor), a program and data memory unit, input/output (I/O) interfaces, communication interfaces, and a power supply. The I/O interface connects the PLC with input devices such as sensors and switches, and output devices such as actuators. The communication interfaces enable the PLC to communicate with other devices on the network, including a human-machine interface (HMI), an engineering workstation, a programming device, and other PLCs. The proposed technique captures timing information for each controller in a non-invasive manner by analysing messages exchanged between PLCs. It estimates the scan cycle time based on these message exchanges to generate timing-based fingerprints unique to each PLC, enabling authentication and detection of attacks on disseminated messages.
Sector
This technology falls under the Security of Critical Infrastructure sector, specifically focusing on Industrial Control Systems. Our invention is applicable to water treatment and distribution systems, as well as oil and gas infrastructures, and the approach can be extended to electric grids and other distributed control systems.
Market opportunity
The global market for Industrial Control Systems (ICS) security is a substantial and growing market opportunity, valued at approximately USD 19.24 billion in 2025. This market is projected to expand significantly, with forecasts estimating it will reach a size of over USD 32 billion by 2030, growing at a compound annual growth rate (CAGR) of around 8-10%.
Applications
The technology is applicable for intrusion detection in critical infrastructure environments such as water treatment plants, electric power grids, autonomous transportation systems and other Industrial Control Systems where secure and reliable controller authentication is required.
Customer benefits
Unlike traditional intrusion detection methods that depend primarily on network traffic analysis, this solution creates a unique fingerprint for each PLC based on its intrinsic operational characteristics. This allows for more robust authentication and enhances the ability to detect spoofing and advanced network attacks.
Technology readiness level
TRL 4
Ideal collaboration partner
Ideal collaboration partners include:
- Critical infrastructure owners and operators: these include water utilities, energy grid operators, and oil & gas companies that manage large-scale operational technology (OT) environments. Their involvement provides access to real-world systems for validation and ensures that our solutions address practical resilience challenges in sectors of national importance.
- OT cybersecurity vendors seeking advanced capabilities: many current ICS security products focus primarily on network-layer monitoring. Our technology offers a complementary approach by leveraging process-level data for anomaly detection and predictive resilience. Partnering with these vendors enables integration into existing platforms, creating differentiated offerings that go beyond traditional perimeter defenses.
These partnerships will not only accelerate technology readiness but also foster co-created standards, joint demonstrators, and pathways to commercialisation.
Collaboration mode
This technology is suitable for multiple collaboration modes, including R&D collaboration, licensing, and IP acquisition.
