SUTD Student Discovers "High Severity" Security Flaws in 5G Qualcomm Chips
A security flaw which could have wiped out 5G connection for about 59% of the world’s mobile phones was recently discovered by a recent Singapore University of Technology and Design (SUTD) PhD graduate student.
The vulnerability findings, tracked as CVE-2023-33044, CVE-2023-33043 and CVE-2023-33042, involved Qualcomm’s 5G chips, which are used in popular phone models like Apple, Asus and Samsung. As many as 714 smartphone models from 24 brands were impacted, including those from Vivo, Xiaomi, OPPO, Samsung, Honor, Motorola, realme, OnePlus, Huawei, ZTE, Asus, Sony, Meizu, Nokia, Apple and Google. It was discovered by Dr Matheus E. Garbelini when he was a PhD graduate student in SUTD under the Singapore International Graduate Award1 (SINGA) scholarship. He is now a research fellow in SUTD.
Using a process known as Wireless Fuzzing to test Qualcomm's chips for flaws in its firmware, Dr Garbelini, with SUTD PhD student Mr Zewen Shang, SUTD research group member Assistant Professor Sudipta Chattopadhyay and collaborators from the Agency for Science, Technology and Research’s (A*STAR) Institute for Infocomm Research (I2R), Dr Sumei Sun and Dr Ernest Kurniawan, discovered that malicious attacks sent from a rogue standalone 5G base station (gNodeB) could trigger a "Denial of Service" (DoS) attack, causing a 5G connection loss for the mobile phone. The 5G connection cannot be recovered even after the attack has stopped, and the only way to recover the connection is through manually rebooting the phone and sometimes even requires removing and reinserting the SIM card.
"With the adoption of 5G smartphones increasing, these findings are significant because 5G is slated to be the next generation of wireless technology. For now, although there are no known defence against attacks exploiting these flaws, users should still keep their Android OS and iOS patched to the latest versions of the phone software as most security issues are done during these updates," said Dr Garbelini.
Qualcomm, which is the largest supplier of such chips, commended the SUTD team for the discovery. Its spokesperson said: "Developing technologies that endeavour to support robust security and privacy is a priority for Qualcomm Technologies. We commend Matheus Garbelini and Sudipta Chattopadhyay from SUTD for using coordinated disclosure practices, and we have worked with them to address the issues affecting some 5G modems. Patches were made available to OEMs in August 2023, and we encourage end users to apply security updates as they become available from device makers."
In recognition of his efforts, Qualcomm has awarded Dr Garbelini US$17,000 for discovering three “high severity” flaws in their 5G chips including the Qualcomm X55/X60. These vulnerabilities fall under the larger class 5Ghoul recently found by Dr Garbelini.
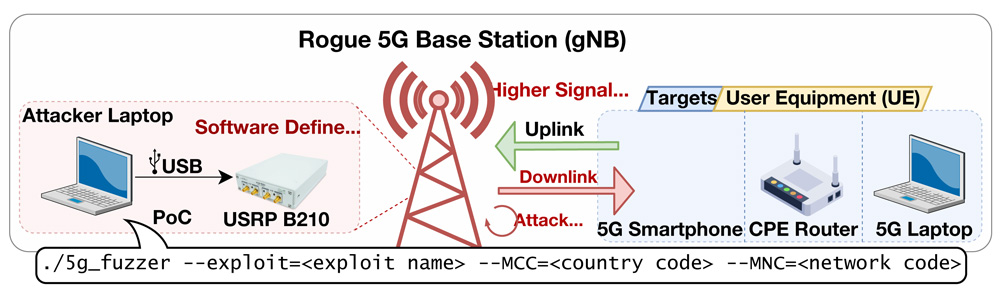 An overview of the 5Ghoul attack process. Once a target is connected to the rogue base station (gNB), the attacker simply launches the exploit script as shown in the command prompt with the Mobile Country Code (MCC) and the Mobile Network Code (MNC).
An overview of the 5Ghoul attack process. Once a target is connected to the rogue base station (gNB), the attacker simply launches the exploit script as shown in the command prompt with the Mobile Country Code (MCC) and the Mobile Network Code (MNC).
1 The Singapore International Graduate Award (SINGA) is a collaboration between the Agency for Science, Technology & Research (A*STAR), the Nanyang Technological University (NTU), the National University of Singapore (NUS), the Singapore University of Technology and Design (SUTD) as well as the Singapore Management University (SMU).